Medical practices face a complex puzzle when planning backup retention for HIPAA compliance. Unlike other industries with straightforward “delete after X years” rules, healthcare organizations must balance federal HIPAA requirements, state medical record laws, and practical operational needs.
This guide breaks down retention requirements in plain language, helping practice managers create defensible backup policies without getting lost in technical jargon.
Understanding the Three-Layer Retention Challenge
HIPAA doesn’t set a single backup retention period. Instead, your practice must satisfy three overlapping requirements:
HIPAA Documentation Retention (6-Year Rule) Under the Security Rule, you must keep HIPAA-related documentation for at least six years from creation or last effective date. This includes policies, risk assessments, Business Associate Agreements, audit logs, and breach investigation records.
Medical Record Retention (State Law) Most states require medical records to be kept 7-10 years for adults, and until age 21-28 for minors. Some specialties like oncology may have longer requirements. These laws typically override shorter retention periods.
Operational Recovery Needs Beyond compliance, your practice needs recent backups for day-to-day recovery from ransomware, system failures, or user errors. These short-term backups don’t need decade-long retention but must be reliable and tested.
What Types of Data Need Long-Term Retention?
Not all backup data requires the same retention period. Here’s how to categorize your practice’s information:
Core Medical Records
- Patient charts and clinical notes: Follow state requirements (typically 7-10 years)
- Diagnostic imaging: Often 7-10 years, longer for certain specialties
- Laboratory results: Usually tied to medical record retention periods
- Medication records: 7-10 years or state-specified periods
For minors, most states extend retention until age of majority plus additional years. A common pattern is keeping pediatric records until age 25-28.
HIPAA Compliance Documentation
- Audit logs and access records: Minimum 6 years, often extended to match medical record retention
- Risk assessments and security policies: 6 years from creation or last update
- Incident response documentation: 6 years from breach or security event
- Training records and workforce access logs: 6 years from employment termination or access change
Business and Billing Records
- Claims and billing data: Often 7-10 years based on Medicare and commercial payor requirements
- Financial records involving PHI: Follow both healthcare and business record retention rules
- Insurance correspondence: Typically 7 years minimum
Building a Practical Backup Retention Strategy
A layered approach balances operational needs with compliance requirements:
Short-Term Operational Backups (30-90 Days)
- Daily incremental backups for recent file changes
- Weekly full backups for complete system restoration
- Purpose: Quick recovery from ransomware, system crashes, or user errors
- Storage: Can use faster, more expensive storage since retention is brief
Medium-Term Recovery Backups (6-12 Months)
- Monthly full backups for broader recovery scenarios
- Purpose: Protection against undetected data corruption or delayed breach discovery
- Storage: Balance between speed and cost
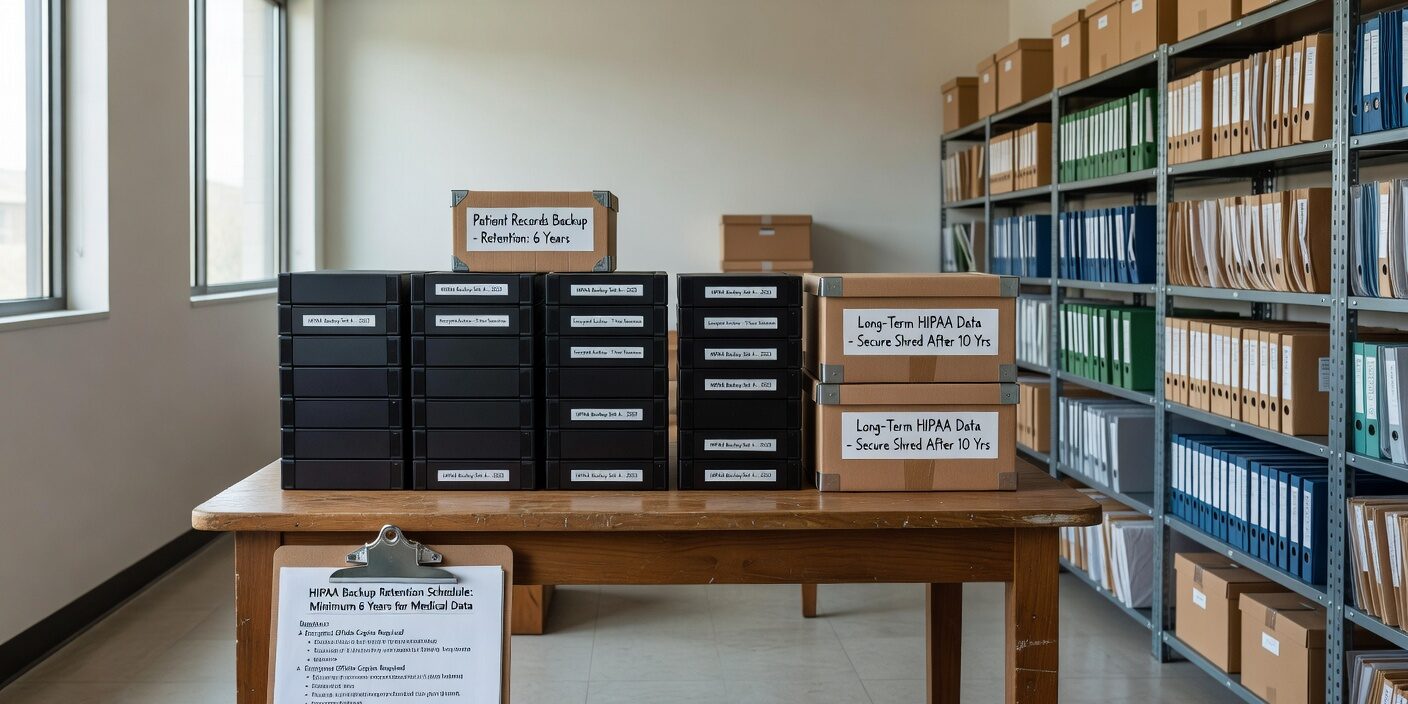
Long-Term Archive Backups (7-10+ Years)
- Quarterly or annual complete snapshots of all systems containing PHI
- Purpose: Meet medical record and HIPAA documentation requirements
- Storage: Can use slower, cost-effective “cold storage” options
- Critical requirement: Must remain readable and retrievable throughout retention period
Compliance Documentation Archives (6-10 Years)
- Separate retention for HIPAA policies, audit logs, and compliance records
- Purpose: Demonstrate ongoing compliance during audits or investigations
- Storage: Secure, tamper-evident systems with detailed access logging
Common Retention Policy Mistakes to Avoid
Assuming EHR Vendor Handles Everything Many EHR providers offer some backup services, but you’re ultimately responsible for meeting retention requirements. Verify exactly what your vendor backs up, how long they retain it, and what happens if you change systems.
No Written Retention Policy OCR expects documented backup and retention procedures. “We keep everything indefinitely” or “We follow best practices” won’t satisfy compliance requirements. Create specific, defensible retention periods for each data category.
Forgetting About System Logs Audit trails and access logs are often overlooked but are crucial for demonstrating HIPAA compliance. These logs must be retained even if the primary systems are upgraded or replaced.
Not Testing Long-Term Restores It’s not enough to create archives—you must periodically verify that old backups are still readable and complete. Storage media degrades, file formats become obsolete, and encryption keys can be lost.
Creating Your Backup Retention Schedule
Start by researching your state’s medical record retention requirements. Then create a simple matrix:
1. List all systems containing PHI (EHR, patient portal, billing system, email, etc.) 2. Determine retention period for each data type based on compliance requirements 3. Map backup strategy to meet the longest applicable retention period 4. Document the rationale for your retention decisions 5. Schedule regular reviews to ensure policies stay current with changing regulations
For most practices, a common pattern emerges: short-term backups for operational recovery, plus long-term archives retained for 7-10 years to satisfy both HIPAA and medical record requirements.
Ensuring Your Backups Stay Compliant Over Time
Long-term retention brings unique challenges:
Technology Evolution Systems and file formats change over time. Your 2024 backup might be unreadable in 2034 without proper planning. Consider format migration strategies and maintain documentation about backup contents and structures.
Secure Storage Throughout Retention Period Backups must maintain HIPAA security safeguards for their entire retention period. This means encryption, access controls, audit logging, and physical security—even for decade-old archives.
Vendor Relationship Changes If you use cloud backup services, ensure your backup and recovery planning for HIPAA-regulated practices includes provisions for data retrieval if you change providers. Business Associate Agreements should specify data return and deletion procedures.
Regular Testing and Validation Test restore procedures annually, especially for long-term archives. Document successful restores and address any issues promptly. This testing provides evidence of due diligence for compliance audits.
What This Means for Your Practice
Successful backup retention for HIPAA requires balancing multiple requirements rather than following a single rule. Focus on creating documented, risk-based policies that satisfy your longest applicable retention requirements while maintaining operational flexibility for short-term recovery needs.
The investment in proper backup retention planning pays dividends during audits, cyber incidents, or legal discovery. Practices with clear, tested retention policies can demonstrate compliance confidence and reduce regulatory risk.
Modern backup solutions can automate much of this complexity, allowing you to set retention rules by data type and automatically transitioning from operational storage to long-term archives. The key is understanding your requirements first, then selecting tools that support your compliance strategy rather than hoping technology alone will solve retention challenges.